| Blog - Comodo One News |
|---|
|
7 Ways RMM Software Can Help Increase Efficiency of IT teamSeptember 28, 2017

Technology today is evolving and multiplying in the enterprise scenario, in complexity as well as in profusion. Today we have the BYOD (Bring Your Own Device) technology, the IoT (Internet of Things) and such other things which have revolutionized everyday infrastructure at the enterprise level. IT management for organizations has changed, drastically with the introduction of mobile technology and personal devices into the work culture and with the issues too becoming very complex and sophisticated. IT is now strategic in any enterprise and the CIO is as important as the CEO or CFO. Learn More |
|
Patch Management for Tackling Ransomware Is Easier Said Than DoneSeptember 19, 2017

In the connected world of today, there are many avenues for cyber criminals to try penetration. The increasing development of ransomware and ransomware-as-a-service has led to massive outbreaks in the number of attacks. Every time a vulnerability has been exposed and an exploit detected, security firms and application developers develop and release appropriate patches to thwart further exploits. Patches are released periodically or as hotfixes. These hotfixes are urgent security patch updates that must be applied without any delay. Learn More |
|
Why You Need To Secure Your Endpoints Comodo ONE BlogSeptember 14, 2017

It raining security threats in the digital world. Security threats which are so severe in nature that they not only bringing the digital world to a standstill but are making us revert back to using papers for carrying out our day-to-day operations as our computers recover from these malicious security attacks. Therefore the need of the hour is to equip our networks using the right combination of security tools which can resist such attacks. Learn More |
|
The Top 3 Free Email Marketing PlatformsSeptember 11, 2017

Email marketing is dead and gone. It's 2017, social media is the best way to engage with your audience. It is 2017, but email marketing is not dying. According to Campaign Monitor, you are 6x more likely to get a click-through from an email campaign than you are from a tweet. Research by Randicati said a message is 5x more likely to be seen in email than through Facebook. In fact, email marketing has an ROI of 3800%. Yes, you read that right, three zeros. Thirty eight thousand. Learn More |
|
And The Academy Goes To...September 11, 2017

In case you missed our recently published press release, we at Comodo have launched a free self-paced and interactive education portal for MSP partners, Comodo Academy. Here, partners are trained and certified on the Comodo ONE platform for IT and security management (ITSM). The online portal contains tutorials, quizzes and practical exams to expand a partner's security knowledge. Learn More |
|
What does Comodo One and iTunes Have in Common?September 11, 2017

Why is Comodo One free? What's the catch? When is my free trial over? The answer: To put it plainly: We, at Comodo One, would like to partner with your MSP business. You don't make any money off of management tools, so why would we charge you for them? Instead, we will help you manage your IT infrastructure. Then, you'll be able to purchase our apps, which you can sell to your clients as part of your successful business services. When you make money, we make money. It's really that simple. Learn More |
|
Pathways to simplify and Speed Up Security Patch UpdatesSeptember 07, 2017

Patches are inevitable security for all software applications. Ensuring updated patch security is possible only through effective patch management. Cyber security threats are constantly evolving. While on one side cyber security professionals are trying to make the internet and IT world more secure, on the other side cyber criminals are trying to find out ways to identify new vulnerabilities and penetrate the defenses to eavesdrop, compromise and steal data. Learn More |
|
Comodo One Endpoint Protection | Stay Ahead of Unknowm ThreatsSeptember 05, 2017
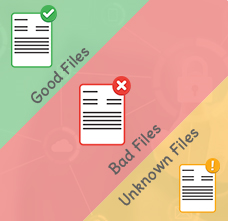
The Comodo One approach denies unknown files defaultly, while also allowing the user to safely access it. Think of it as putting your unknown file in a little jail cell. You can still interact with it, but it's unable to roam freely until it has been deemed good or bad. Comodo One is the only endpoint security solution that automatically handles unknown files and zero-day threats with a default deny approach. Almost all antivirus solutions default allow unknown files, which allows malware to go into the system/network completely undetected. Learn More |
|
Specialized Threat Analysis and Protection(STAP) | Comodo OneSeptember 05, 2017

Cybersecurity, like all technology, is constantly changing. Step by STAP. If you don't know what STAP is here's the lowdown: it's a term IDC coined that stands for Specialized Threat Analysis and Protection. STAP is meant to detect zero-day attacks and data exfiltration by attackers, which can go on undetected for weeks, if not years. Basically, it's a new category of security products which aim to defend against specialized threats that have emerged over the last couple years. Learn More |
|
How to Convince Your Break-Fix Clients to Sign Up For MSP?September 01, 2017

Transitioning your break-fix clients to managed services can be a challenge. Most people live by the 'if it ain't broke, don't fix it' rule. Why? Because people don’t like to spend money on what-ifs. Usually... Americans spend thousands of their hard-earned dollars on auto collision insurance annually. In reality, the average person is far more likely to have their computer crash than their car. Rationally, the SMB owner knows that to get the most out of their network, it needs to be monitored and maintained. But when it's time to part with their money in order to prevent something that might happen, suddenly they tighten their purse strings. Learn More |
|
Basic Tools for True Managed Service Provider(MSP)September 01, 2017

With a new major cyber attack hitting computers worldwide every week, business owners are wondering if there are any safe zones in cyber warfare. While some businesses are at a larger risk than others, everyone needs some kind of internet protection. That's where you come in. Managed Service Provider to the rescue! But are you a true MSP? There are basic tools you need to employ in order to truly fit the mold and ensure your business is secure from hackers' reach. Learn More |